Blog

The Silent IT Budget Killer
Most business owners treat their IT budget like a gym membership in January … they sign up, pay every month, and never check if they’re actually getting results. That’s why so many companies…

This Is How IT Fails
Let me tell you the truth about IT problems. They don’t show up on slow Mondays when everyone’s in a good mood. They hit at the exact moment you can’t afford them ……

Is Your Office Quietly Leaking Data?
As August rolls in and summer starts to wind down, it’s the perfect time to get back into a steady routine. That includes refreshing the habits that keep your digital workspace safe. The…
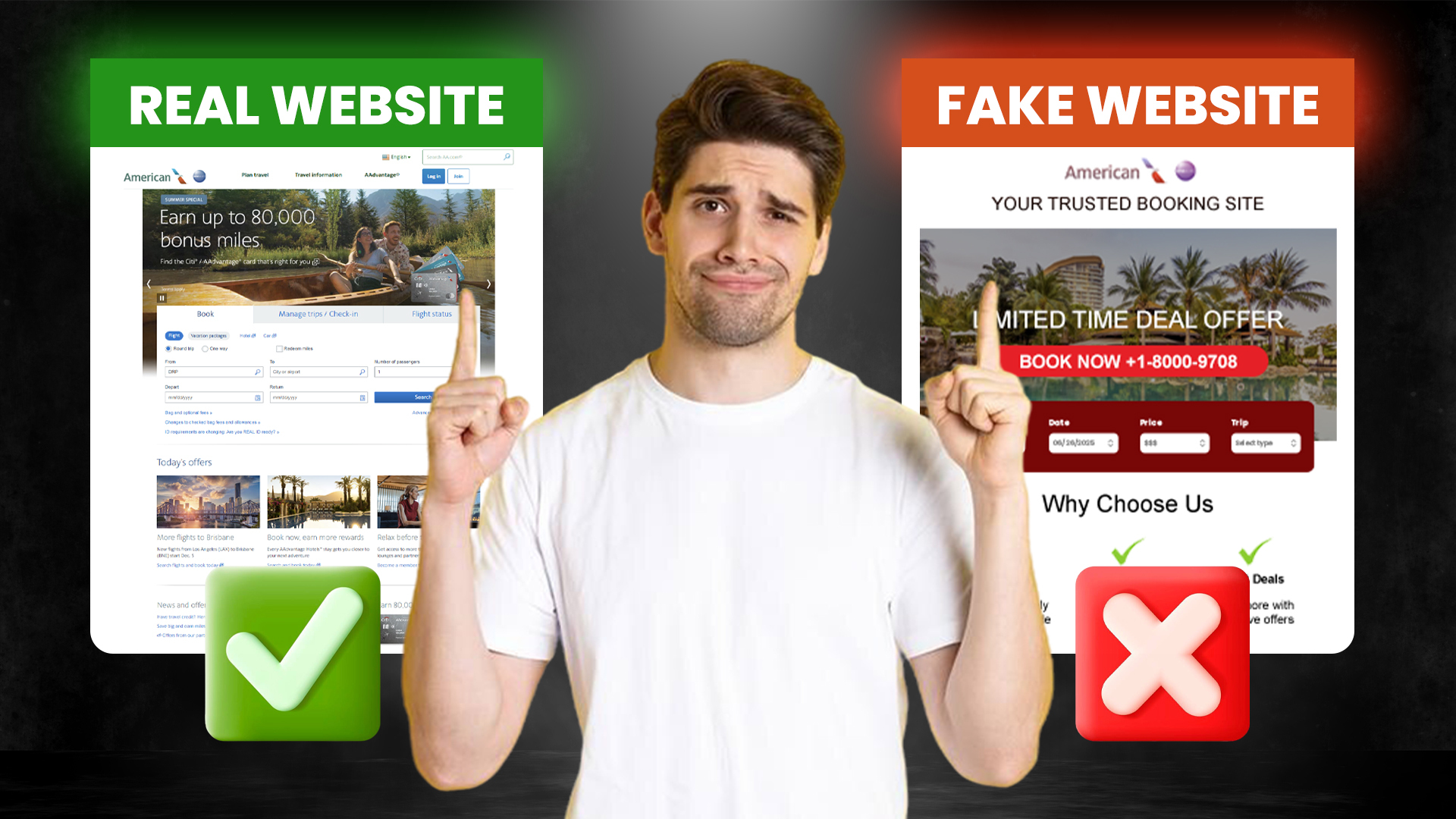
The One Click That Could Ruin Your Vacation
Just because summer is winding down doesn’t mean the travel risks are. Whether you’re squeezing in one last vacation or planning a Labor Day escape, it’s good to stay alert. Cybercriminals are always…
How Can We Help?
Call us at (916) 441-3838 or complete the form below and we'll help in any way we can.
"*" indicates required fields
Featured Posts
Blog | 09.03.2026
This Is How You Kill Productivity
Blog | 02.03.2026
The Next Big Threat Waiting at Your Digital Door



